Security Strategies for the Quantum Era: How Different Industries Are Preparing for QuantumThreats
April 4, 2026 Adrita Rahman Prapti Roy
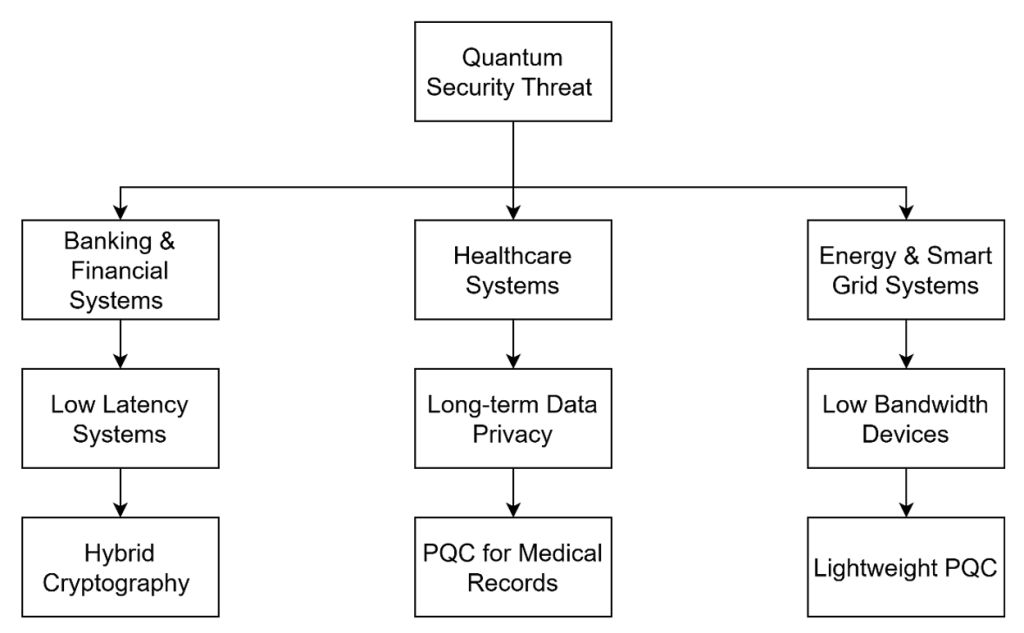
Cybersecurity relies heavily on cryptographic algorithms to protect sensitive information. Modern systems, from banking to energy grids, depend on public-key cryptography for secure data exchange. However, quantum computing poses a major threat. Unlike classical computers, quantum machines use qubits, allowing them to solve certain problems much faster. Notably, Shor’s algorithm can break widely used encryption […]
Read More
HOW GRAPH THEORY BENEFITS ANALYST IN OSINT USING MALTEGO
March 30, 2026 Adrita Rahman Sreejonty Chakraborty
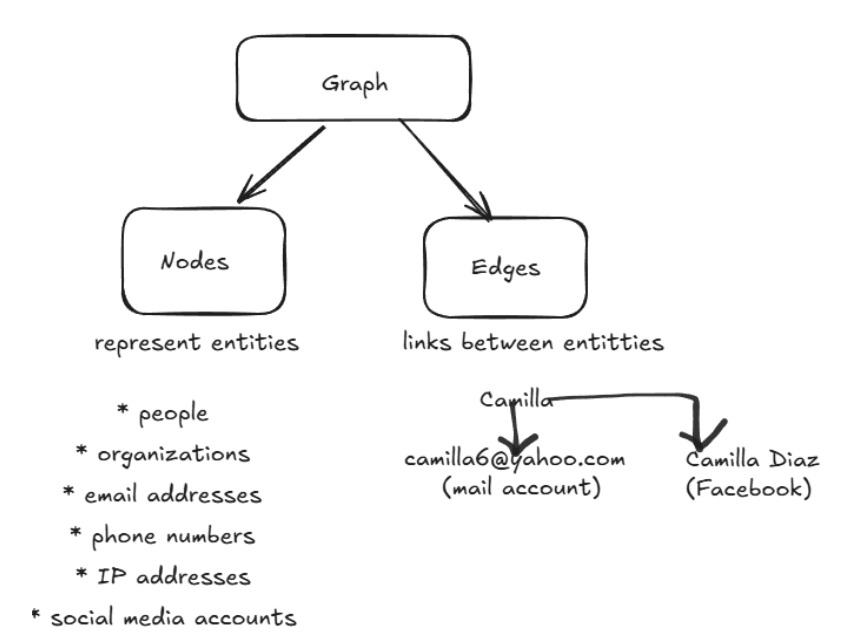
OSINT investigations involve analyzing large volumes of interconnected data such as domains, IP addresses, emails, and identities. Analysts deal with such fragmented and highly interrelated data. However, the challenge is not data collection, but identifying meaningful relationships across entities. And graph-based approaches allow analysts to visualize and explore these relationships effectively. Tools like Maltego operationalize […]
Read More
A Study of HTTP, HTTPS & Network Safety
March 12, 2026 Adrita Rahman Ayesha Siddika
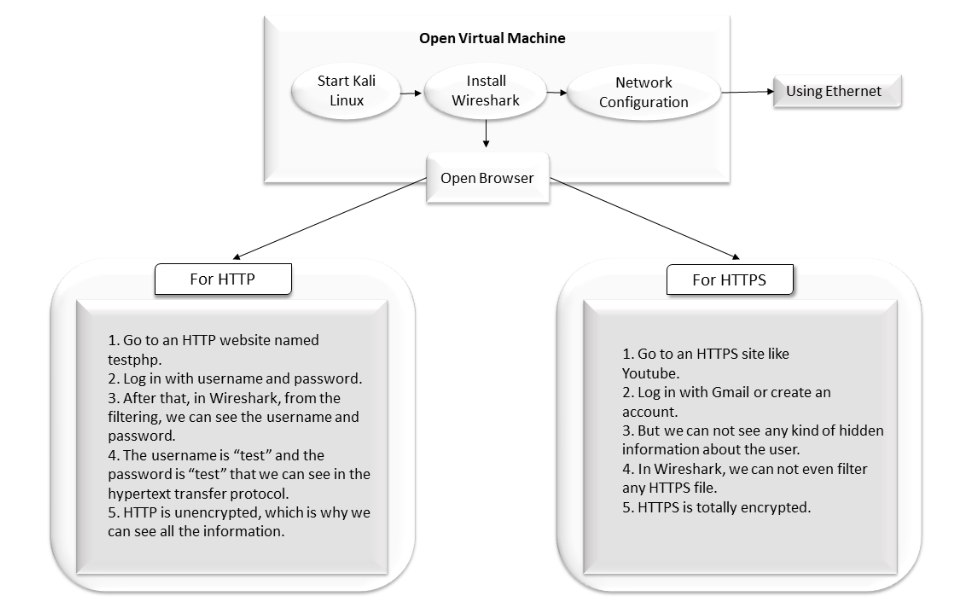
Network Security Research focuses on developing and improving technologies that protect computer networks and the data they transmit. It involves studying security practices, policies, and defensive mechanisms to safeguard networks from unauthorized access, data breaches, and misuse. This research analyzes vulnerabilities and contributes to the development of stronger security protocols that help protect sensitive information […]
Read More
Network Discovery with Nmap: Finding Local Devices
March 2, 2026 Adrita Rahman Istiyak Hasan Maruf, Uncategorized
Network discovery is a fundamental aspect of cybersecurity and ethical hacking. Understanding what devices exist on a network, what services they run, and what potential vulnerabilities they expose is essential for maintaining a secure digital environment. In this blog post, we document our hands-on experience setting up a Kali Linux virtual machine and using Nmap […]
Read More
How to Use OWASP ZAP to Automatically Scan and Test Web Vulnerabilities.
December 7, 2025 Adrita Rahman Rifa Sanjida
The article describes how ZAP can help new and experienced security testers investigate how websites are secured and compromised. Since Kali Linux already has most of the security tools, it served as the primary environment for this experiment. DVWA (Damn Vulnerable Web Application) was set up as a deliberately weak web app for vulnerability testing. […]
Read More
From Input to UNION: DVWA SQL Injection Case Study in 2025
December 1, 2025 Adrita Rahman Jannatul Masruk Mukta
What is SQL Injection? SQL Injection (SQLi) is a cyber attack technique that allows an attacker to interfere with the queries that an application makes to its database.It happens when untrusted user input is directly included in an SQL query without proper validation or sanitization. Attackers insert malicious SQL code into input fields(login form,URL parameter).If […]
Read More
Understanding LLM Injection: A Growing Threat in AI Security
November 11, 2025 Adrita Rahman Sadia Afrin
What is LLM injection? LLM injection (Large Language Model injection) is a type of prompt attack where an attacker manipulates a model like ChatGPT by inserting hidden or malicious instructions into the input or data it processes. These instructions can make the model ignore its original rules, leak confidential information, or perform unintended actions. There […]
Read More
Passkeys 101: Why Your Next Login Won’t Need a Password
July 16, 2025 Adrita Rahman Uncategorized
Passwords are the weakest link in most cybersecurity systems. According to Verizon’s 2024 Data Breach Report, over 80% of breaches involve stolen…
Read More
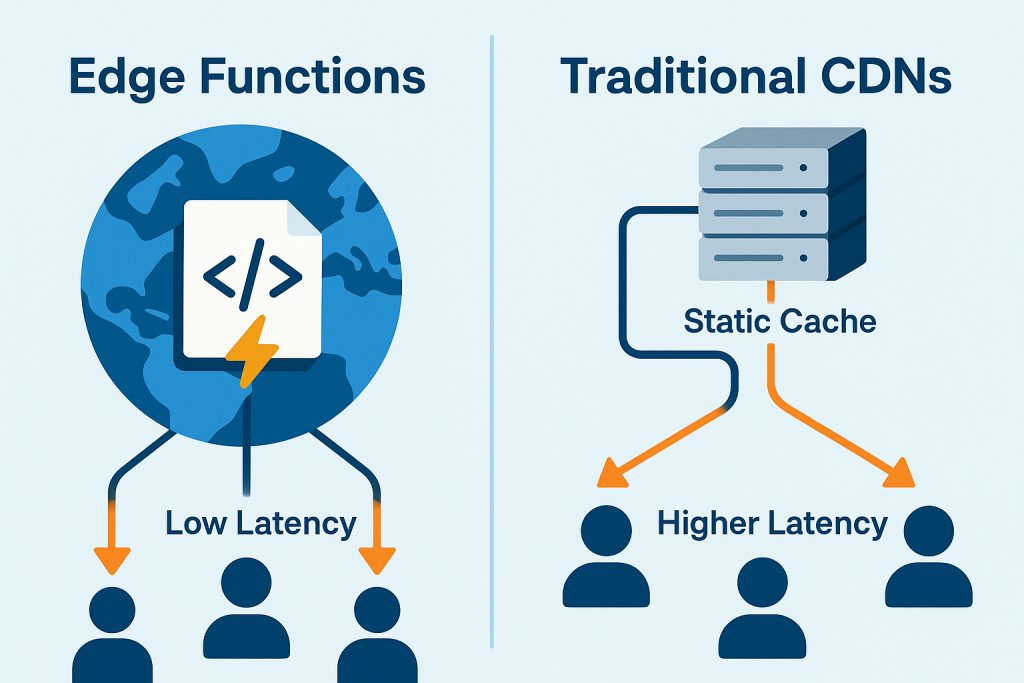
Edge Functions vs. Traditional CDNs: What You Need to Know
July 15, 2025 Adrita Rahman Adrita Rahman
Did you know that modern edge computing services like Cloudflare Workers and Deno Deploy are reshaping the way we deliver web content? …
Read More
Quantum Computing: From Theory to Revolutionary Applications
June 21, 2025 Adrita Rahman Adrita Rahman, Quantum Computer
Quantum computing represents one of the most transformative technological frontiers of our time, promising to solve problems that would take classical …