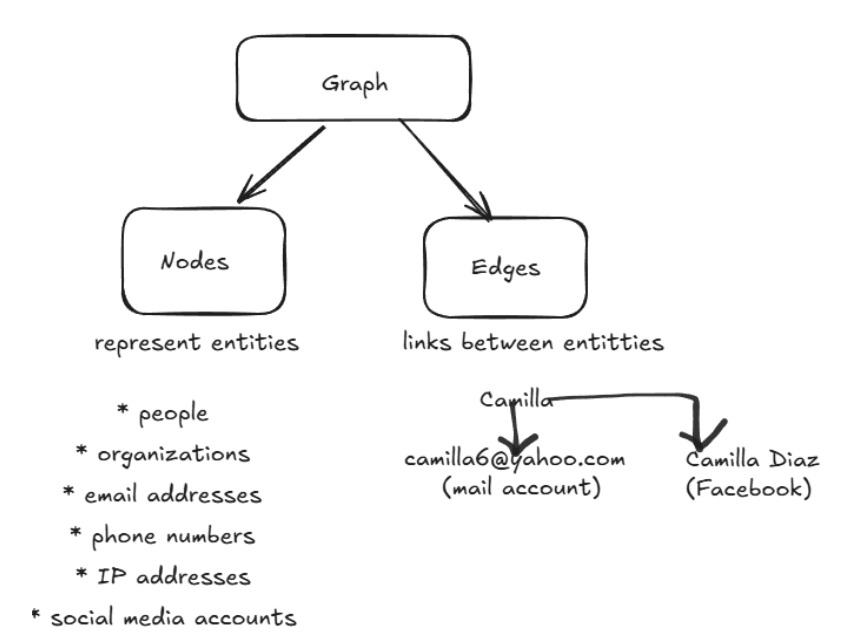
HOW GRAPH THEORY BENEFITS ANALYST IN OSINT USING MALTEGO
March 30, 2026 Adrita Rahman Sreejonty Chakraborty
OSINT investigations involve analyzing large volumes of interconnected data such as domains, IP addresses, emails, and identities. Analysts deal with such fragmented and highly interrelated data. However, the challenge is not data collection, but identifying meaningful relationships across entities. And graph-based approaches allow analysts to visualize and explore these relationships effectively. Tools like Maltego operationalize […]
Read More
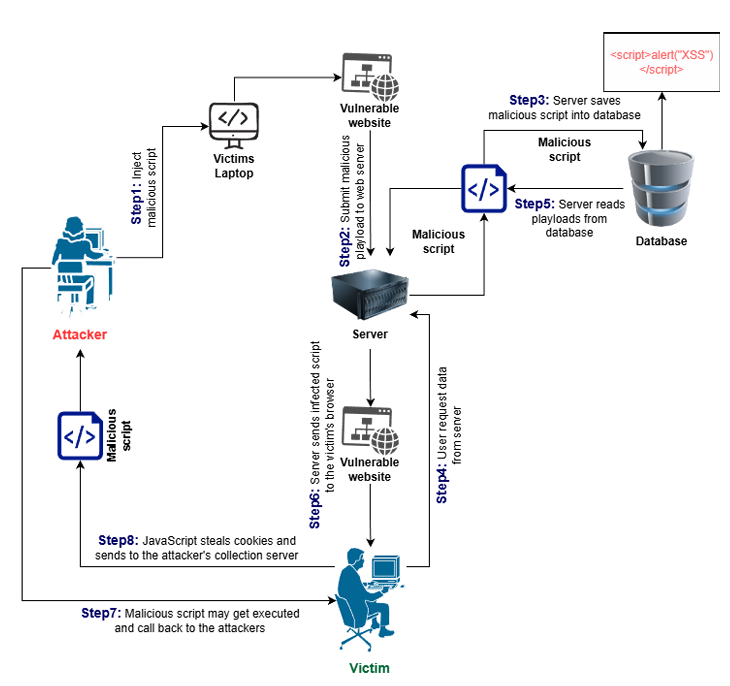
Understanding XSS in depth: Practical Attacks and Analysis using DVWA
March 18, 2026 Towfiqur Rahman Sadia Mehrin Rahi
Cross-Site Scripting is a security vulnerability which is commonly found in web applications that allows attackers to inject malicious scripts (usually JavaScript) into web pages that are viewed by other users. When a victim visits the hacked page, their browser executes the attacker’s code, without realizing it. Three Types of XSS Attacks There are three […]
Read More
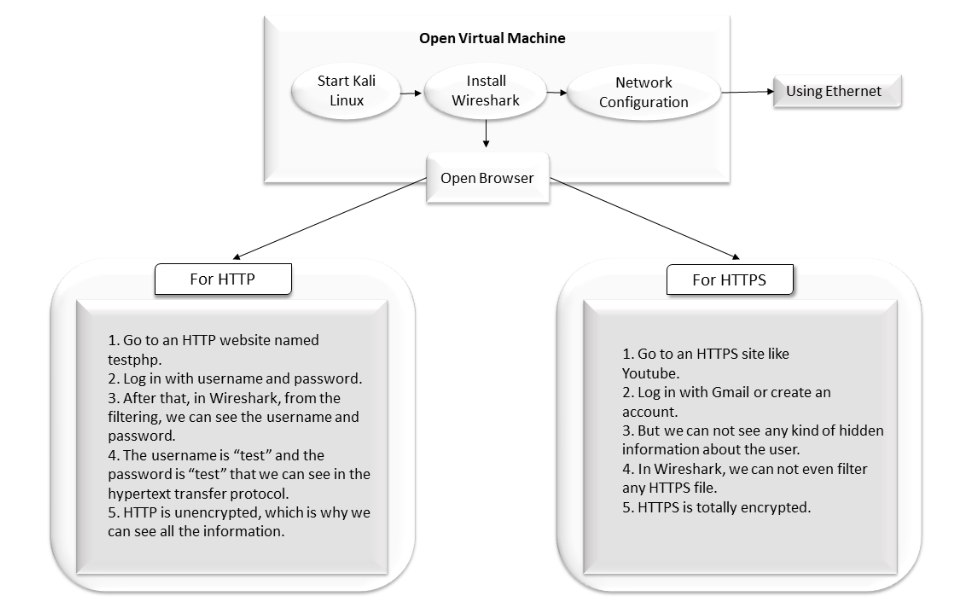
A Study of HTTP, HTTPS & Network Safety
March 12, 2026 Adrita Rahman Ayesha Siddika
Network Security Research focuses on developing and improving technologies that protect computer networks and the data they transmit. It involves studying security practices, policies, and defensive mechanisms to safeguard networks from unauthorized access, data breaches, and misuse. This research analyzes vulnerabilities and contributes to the development of stronger security protocols that help protect sensitive information […]
Read More
Network Discovery with Nmap: Finding Local Devices
March 2, 2026 Adrita Rahman Istiyak Hasan Maruf, Uncategorized
Network discovery is a fundamental aspect of cybersecurity and ethical hacking. Understanding what devices exist on a network, what services they run, and what potential vulnerabilities they expose is essential for maintaining a secure digital environment. In this blog post, we document our hands-on experience setting up a Kali Linux virtual machine and using Nmap […]