Cybersecurity relies heavily on cryptographic algorithms to protect sensitive information. Modern systems, from banking to energy grids, depend on public-key cryptography for secure data exchange. However, quantum computing poses a major threat. Unlike classical computers, quantum machines use qubits, allowing them to solve certain problems much faster. Notably, Shor’s algorithm can break widely used encryption like RSA and ECC [1].
In response, researchers are developing post-quantum cryptography (PQC)—new algorithms designed to resist quantum attacks [2]. As industries transition to quantum-safe security, they must balance this shift with their specific operational constraints.
This article examines the risks of quantum computing, the role of PQC, and how key industries are preparing.
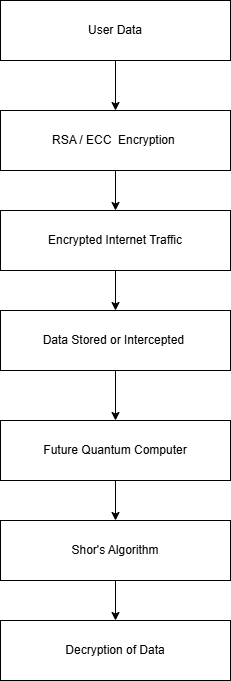
Fig1 : shows how encrypted data collected today could be decrypted in the future using quantum computers
Most modern digital security systems rely on public-key cryptography, particularly RSA and Elliptic Curve Cryptography (ECC). These systems are considered secure because they are based on mathematical problems that are extremely difficult for classical computers to solve—RSA on integer factorization and ECC on the elliptic curve discrete logarithm problem.
However, Shor’s algorithm poses a direct threat to these systems [2]. Using a sufficiently powerful quantum computer, Shor’s algorithm can efficiently solve both mathematical problems, meaning RSA and ECC could be broken relatively quickly once large-scale quantum computers become operational.
Another major concern is Harvest Now, Decrypt Later (HNDL), where adversaries collect encrypted data today and store it until quantum computers can decrypt it in the future. This approach threatens sensitive long-term data such as financial records, medical histories, and government communications.
Therefore, even though quantum computers are not yet powerful enough to break current encryption, organizations must start preparing now.
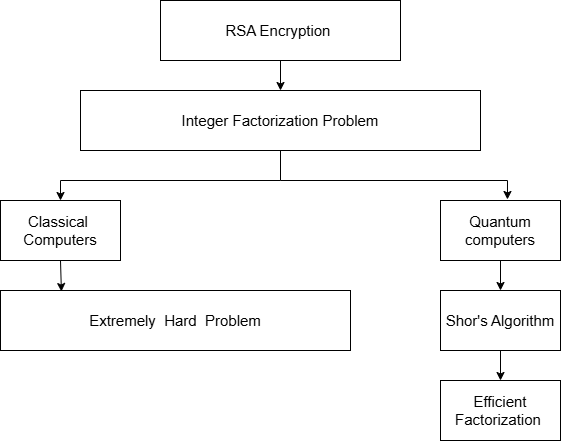
Fig 2 : illustrates how quantum algorithms can solve problems that are extremely difficult for classical computers.
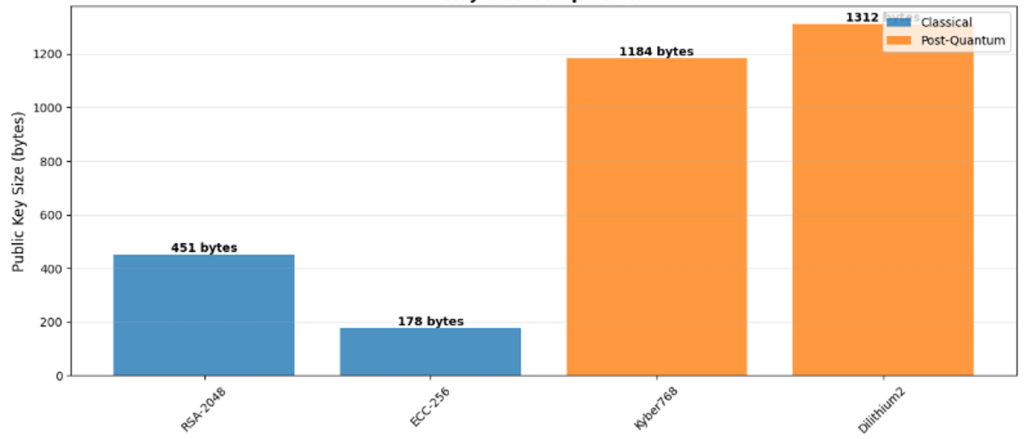
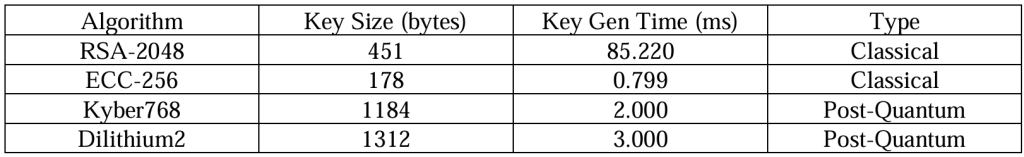
To understand the practical implications of post-quantum cryptography, this experiment compares classical algorithms (RSA-2048, ECC-256) with PQC algorithms (Kyber768, Dilithium2) in terms of key size and key generation time. While PQC algorithms generally require larger key sizes than classical systems, they remain computationally efficient and suitable for integration into modern security protocols.
The experimental results highlight the trade-off between security and performance that must be considered when deploying PQC in real-world systems.
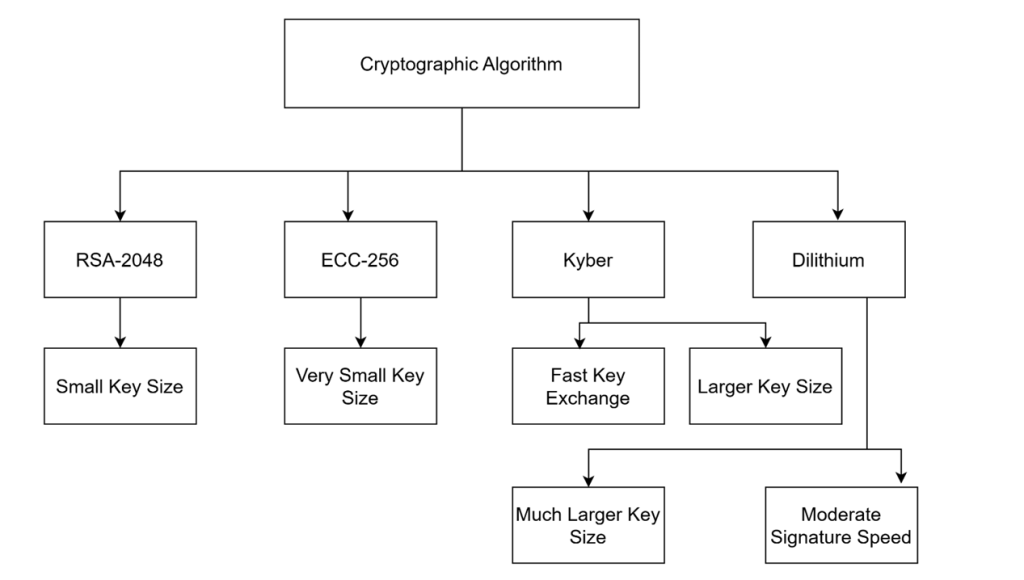
Fig 3 : Compares classical and post-quantum cryptographic algorithms.
Public key size comparison between classical (RSA, ECC) and post-quantum (Kyber, Dilithium) algorithms.
To measure public key sizes, RSA-2048 and ECC-256 keys were generated using Python’s cryptography library, while Kyber768 and Dilithium2 keys were generated using the OQS (Open Quantum Safe) library.
For RSA and ECC, the public keys were serialized in PEM format, which is the standard representation used in real-world applications such as TLS certificates. For Kyber and Dilithium, the raw byte arrays were used as returned by the OQS library.
The results show that RSA-2048 produces a 451-byte public key, while ECC-256 produces a much smaller 178-byte key. In contrast, Kyber768 generates a 1184-byte key and Dilithium2 generates a 1312-byte key. This indicates that post-quantum algorithms require approximately 3 to 7 times larger public keys than classical algorithms.
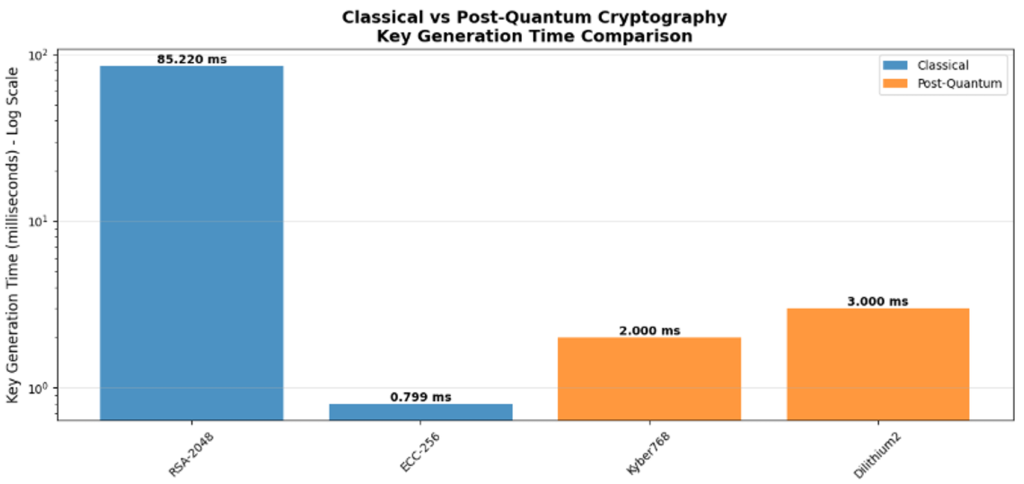
Key generation time comparison showing performance characteristics
Key generation time was measured using Python’s time.time() function, which records the elapsed time with microsecond precision. Each key pair was generated in a single execution, and the total time was recorded in milliseconds for better readability.
RSA-2048 took 85.22 milliseconds to generate, making it the slowest among all tested algorithms. ECC-256 was the fastest, completing in just 0.80 milliseconds. Kyber768 and Dilithium2 demonstrated efficient performance, taking 2.00 milliseconds and 3.00 milliseconds respectively.
These results show that while RSA suffers from significant latency, both post-quantum algorithms perform competitively, comparable to the speed of ECC.
When comparing both experiments, a clear trade-off between security and practical implementation becomes evident.
Classical algorithms like ECC-256 work by leveraging the elliptic curve discrete logarithm problem, which is computationally difficult for classical computers but vulnerable to quantum attacks using Shor’s algorithm. Its strength lies in compact key sizes (178 bytes) and excellent speed (0.8 ms), making it ideal for resource-constrained devices like IoT sensors and mobile phones. However, its weakness is its complete vulnerability to large-scale quantum computers.
RSA-2048 relies on the integer factorization problem. While it is widely adopted in legacy systems such as SSL/TLS certificates and secure email (PGP), it suffers from slow key generation (85 ms) and also faces quantum vulnerability. Its main advantage is widespread compatibility, but its disadvantage is poor performance and large computational overhead.
In contrast, post-quantum algorithms are designed to resist both classical and quantum attacks.
Kyber768 operates as a Key Encapsulation Mechanism (KEM) based on lattice-based cryptography, specifically the Module-Learning with Errors (MLWE) problem, which is believed to be quantum-resistant. Its strength is fast key generation (2 ms) and strong security guarantees, while its weakness is a larger public key size (1184 bytes).
Dilithium2 functions as a digital signature scheme, also based on lattice problems, providing quantum-resistant authentication. Its strength includes reliable security and reasonable speed (3 ms), but its weakness is the largest key size among the four (1312 bytes), which may impact bandwidth in constrained networks.
Overall, classical algorithms offer efficiency and small key sizes but are fundamentally insecure in the quantum era. Post-quantum algorithms provide future-proof security at the cost of larger keys, though their performance remains acceptable for most applications.
This comparison suggests that while transitioning to PQC will require adjustments to storage, bandwidth, and legacy systems, the trade-off is manageable, making PQC a practical and necessary step toward securing digital infrastructure in the quantum era.
Post-Quantum Cryptography (PQC)
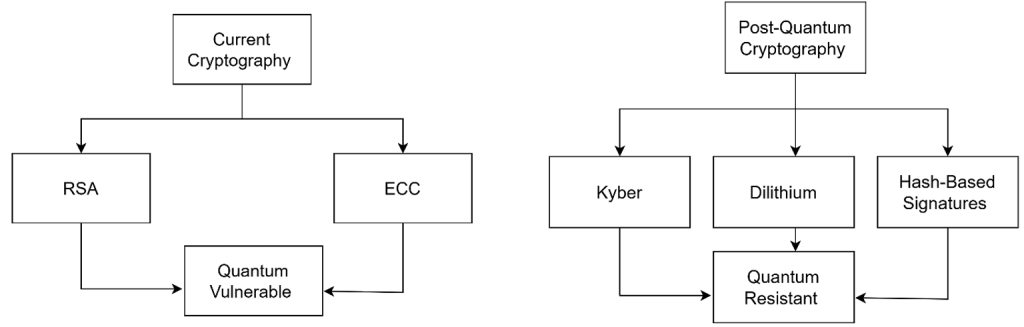
Post-quantum cryptography (PQC) refers to algorithms designed to remain secure against both classical and quantum attacks. Unlike quantum cryptography methods such as QKD, PQC algorithms run on traditional hardware, making them easier to integrate into existing systems.
Many PQC algorithms are based on mathematical problems believed to be resistant to quantum attacks [3].
Two widely discussed PQC algorithms are:
- CRYSTALS-Kyber – used for secure key exchange [4]
- CRYSTALS-Dilithium – used for digital signatures [5]
These were selected by NIST as part of its Post-Quantum Cryptography Standardization Project [1].
PQC can be deployed through software updates and integrated into existing protocols like TLS. However, PQC algorithms typically require larger key sizes and more computational resources, which may affect performance in certain systems.
Despite these challenges, PQC is widely considered the most practical solution for preparing digital infrastructure for the quantum era.
Industry Impact
The transition to quantum-safe security will not occur in the same way across all industries. Different sectors face unique technical constraints, operational requirements, and regulatory environments [1].
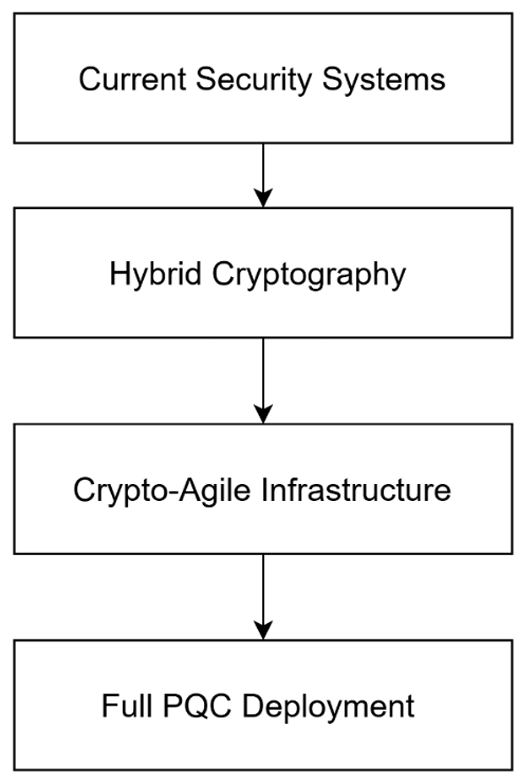
Different industries adopt different security strategies based on operational constraints.
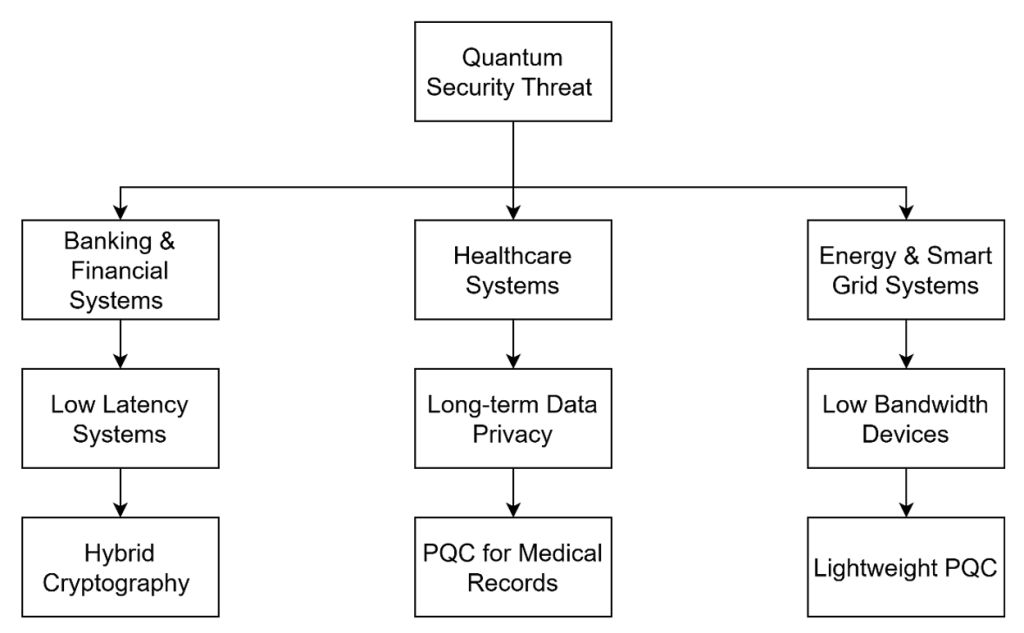
Banking Sector
The banking sector relies heavily on secure digital communication to protect financial transactions, online banking services, and payment systems. Security breaches in this sector can result in significant financial losses and damage to public trust.
One of the key challenges for financial systems is latency sensitivity. High-frequency trading systems operate on extremely short time scales, and even small delays in cryptographic operations can affect performance.
To address quantum threats, many financial institutions are exploring hybrid cryptographic systems, combining traditional algorithms such as RSA or ECC with post-quantum algorithms. Another important strategy is crypto-agility, which allows systems to switch between cryptographic algorithms as needed.
Healthcare Sector
Healthcare systems manage large volumes of highly sensitive data, including patient medical records and diagnostic reports. These records often need to remain confidential for decades, making them particularly vulnerable to long-term quantum threats.
Healthcare organizations are focusing on protecting data at rest and exploring post-quantum encryption for secure storage and communication.
Energy Sector
Energy infrastructure relies on SCADA systems and long-term hardware deployments. These systems often operate with limited computational resources, making the adoption of complex cryptography challenging.
To address this, energy providers are exploring lightweight post-quantum cryptographic solutions and long-term secure infrastructure planning.
The transition to post-quantum cryptography presents both opportunities and challenges. While PQC protects against future quantum attacks, adoption introduces challenges in performance, compatibility, and implementation complexity.
Quantum computing threatens current systems like RSA and ECC. PQC offers a practical solution through quantum-resistant algorithms like Kyber and Dilithium. However, transitioning requires careful planning and crypto-agility.
Early adoption of PQC, combined with flexible system design, will be essential for long-term digital security.
References
[1] National Institute of Standards and Technology (NIST). Post-Quantum Cryptography Standardization Project. https://csrc.nist.gov/projects/post-quantum-cryptography
[2] P. W. Shor, Algorithms for Quantum Computation: Discrete Logarithms and Factoring. Proceedings of the 35th Annual Symposium on Foundations of Computer Science, 1994.
[3] D. J. Bernstein, J. Buchmann, and E. Dahmen. Post-Quantum Cryptography. Springer, 2009.
[4] NIST. CRYSTALS-Dilithium Algorithm Specification (FIPS 203), 2024.
[5] NIST. CRYSTALS-Kyber Algorithm Specification (FIPS 204), 2024.
