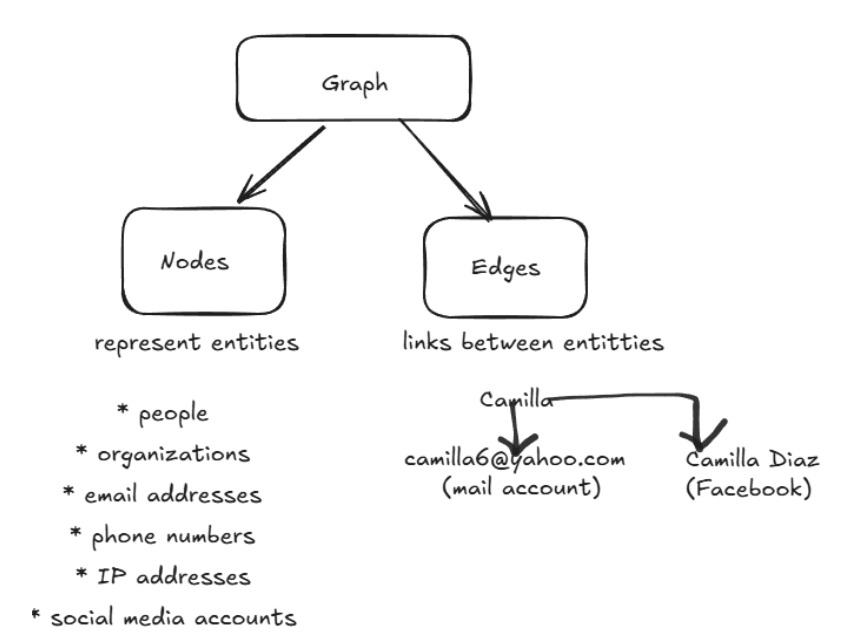
OSINT investigations involve analyzing large volumes of interconnected data such as domains, IP addresses, emails, and identities. Analysts deal with such fragmented and highly interrelated data. However, the challenge is not data collection, but identifying meaningful relationships across entities. And graph-based approaches allow analysts to visualize and explore these relationships effectively. Tools like Maltego operationalize graph theory to support real-time investigation and link analysis.
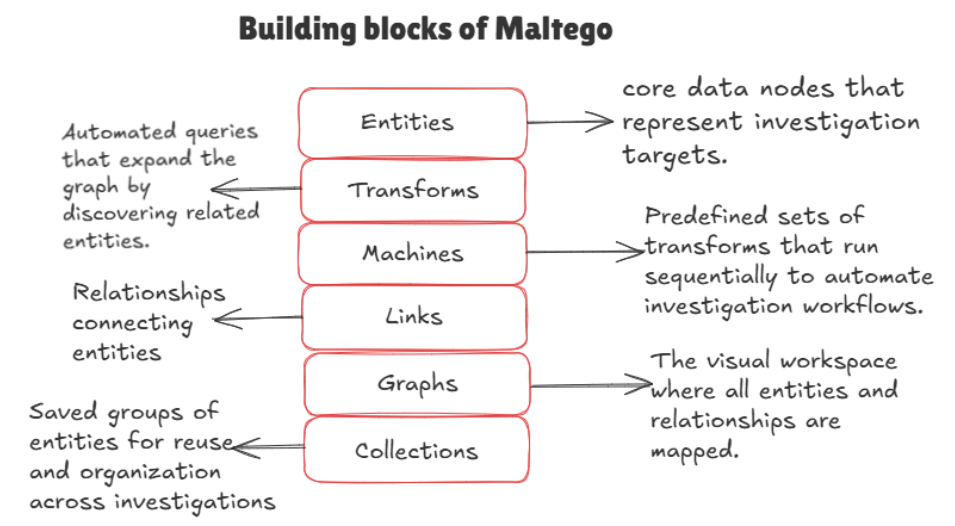
Maltego is an open source tool that allows us to mine and gather information and represent our findings in a meaningful way. We can look up domain names, the network block addresses associated with them, and MX records. With just a few clicks, we can identify key relationships between the objects we insert into our Graph views while Maltego does the data-mining work behind the scenes. Let’s understand the building blocks of Maltego as listed below
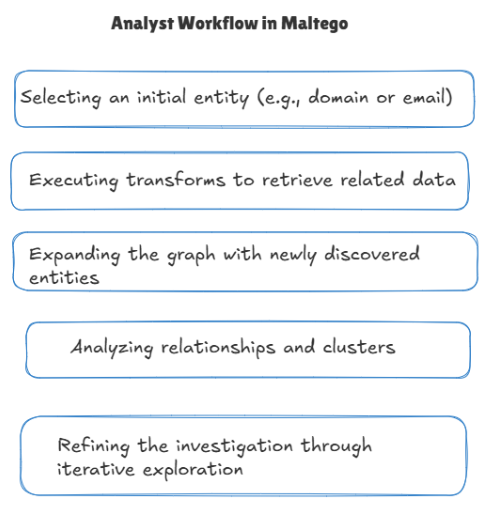
Maltego allows analysts to start with a seed entity (a domain or email) and uses transforms to automatically discover related entities such as IP addresses, infrastructure, and associated identities. The investigation is expanded iteratively, with the graph growing as new relationships are uncovered. Throughout the process, the analyst filters, correlates, and interprets connections to identify meaningful patterns and actionable intelligence.
To demonstrate the practical application of this workflow, a sample investigation was conducted using Maltego. The following figures illustrate how an initial seed entity is progressively expanded through transforms, revealing relationships across infrastructure, services, and associated entities.
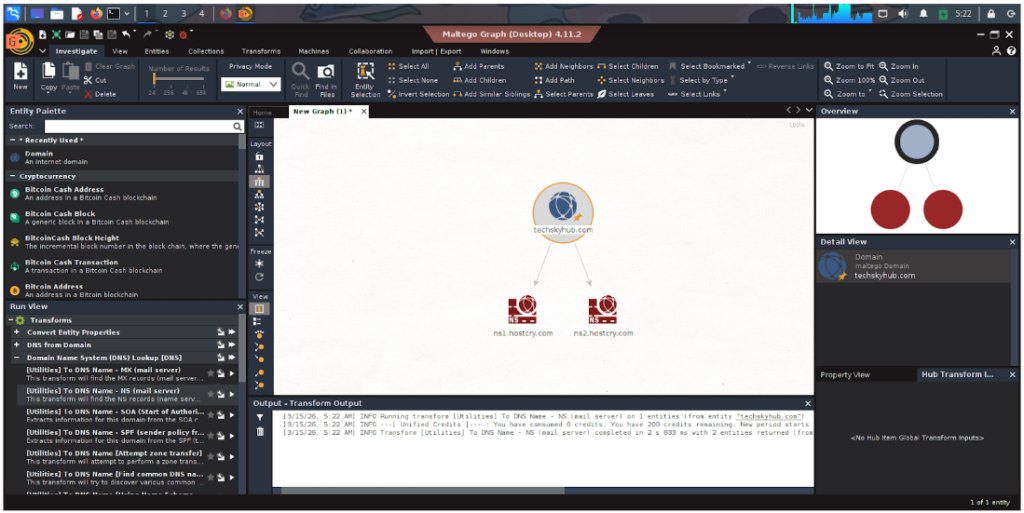
Initial Setup
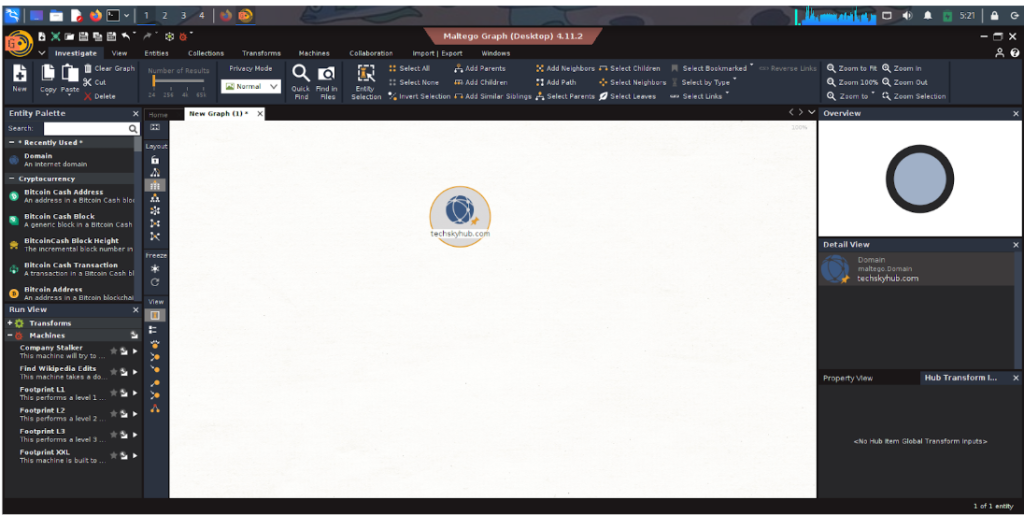
From Infrastructure, click ‘Domain’ and change it to techskyhub.com. At this stage, no relationships are established, and the focus is on defining the target for further expansion.
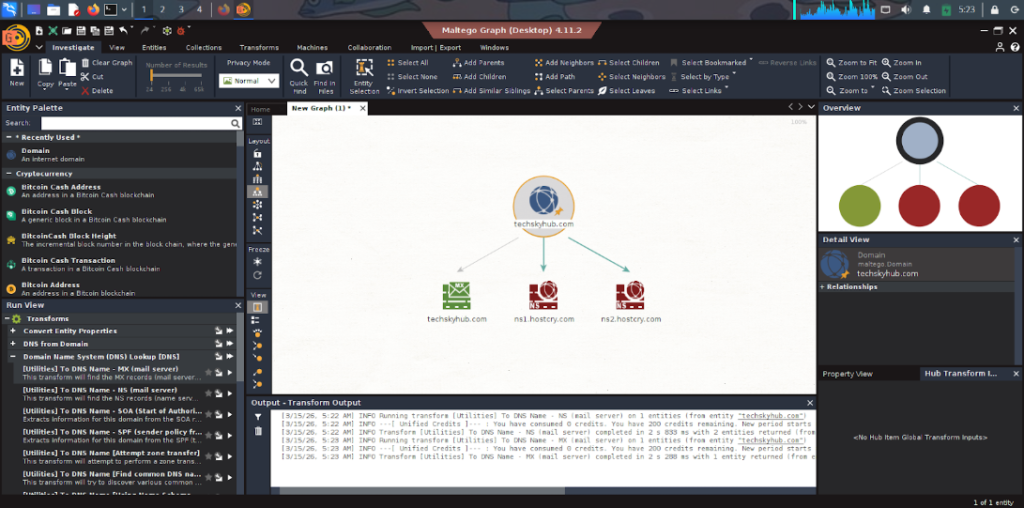
Enumeration of DNS Infrastructure
Click utilities and ns(mail server) and this brings us two name servers. This step helps in understanding hosting dependencies and potential shared services.
Expansion to Mail Server and Services
Click mx(mail server) and this brings us a mail server. This provides insight into communication channels associated with the domain.Such information is useful for identifying possible contact points or phishing vectors.
Infrastructure Correlation via IP Resolution
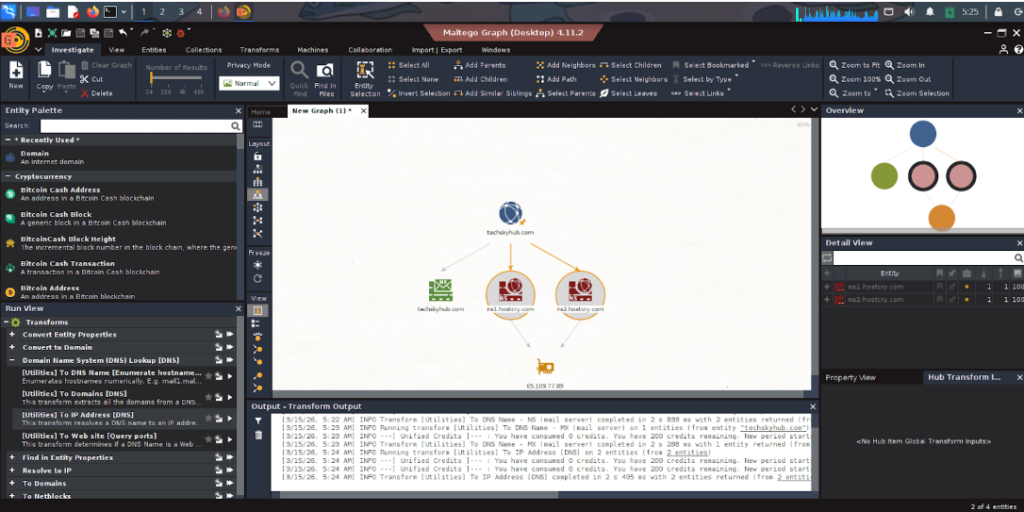
Select two name servers and click “to ip address (dns)” utilities to find their ip address, establishing a direct link between the domain and its hosting server. This allows pivot from domain-based analysis to infrastructure-level investigation, enabling deeper exploration of hosted assets.
Network Range Identification
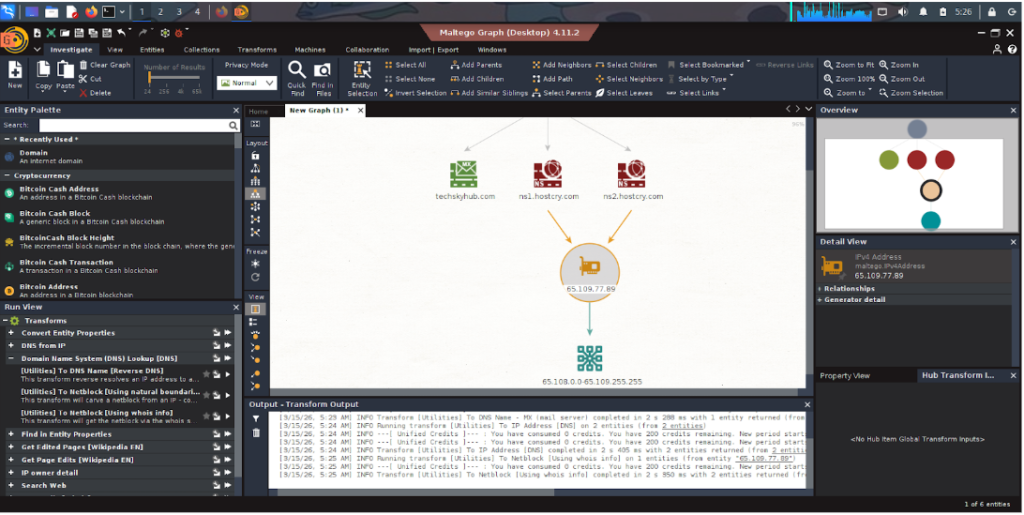
By Selecting the ip address, we can find the netblock by choosing ‘netblock whois info”. This helps to understand the broader network environment and identify other potential assets within the same hosting range, which may indicate shared or related infrastructure.
Entity Filtering and Data Refinement
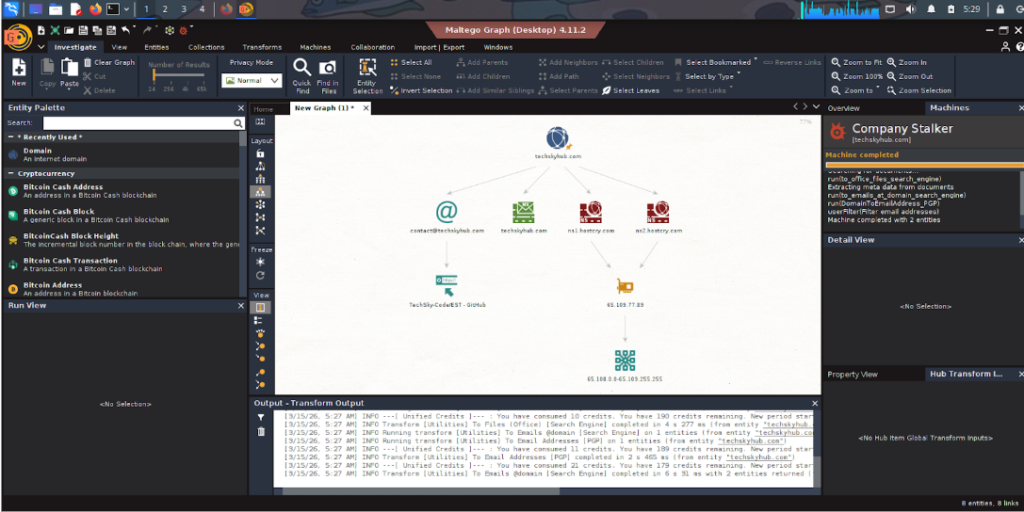
Now using ‘Machine’, we found a mail address and github link related to the domain. This step reflects a critical analytical process—refining the dataset to focus only on meaningful relationships and reducing noise within the graph.
Therefore, this demonstrates how a single seed entity can evolve into a comprehensive graph of interconnected information, enabling analysts to systematically uncover relationships that would be difficult to identify manually. As OSINT data continues to grow in complexity, graph-based tools like Maltego play a critical role in supporting analysts in managing, interpreting, and acting on large-scale intelligence data effectively.
